A security researcher at a Fortune 500 bank recently spent three weeks hunting for vulnerabilities in OpenBSD — the operating system whose entire identity is "we almost never have exploitable bugs." They found nothing. Claude Mythos, Anthropic's newest AI model, found a 27-year-old one in hours. The scan cost under $20,000.
That's where we are now.
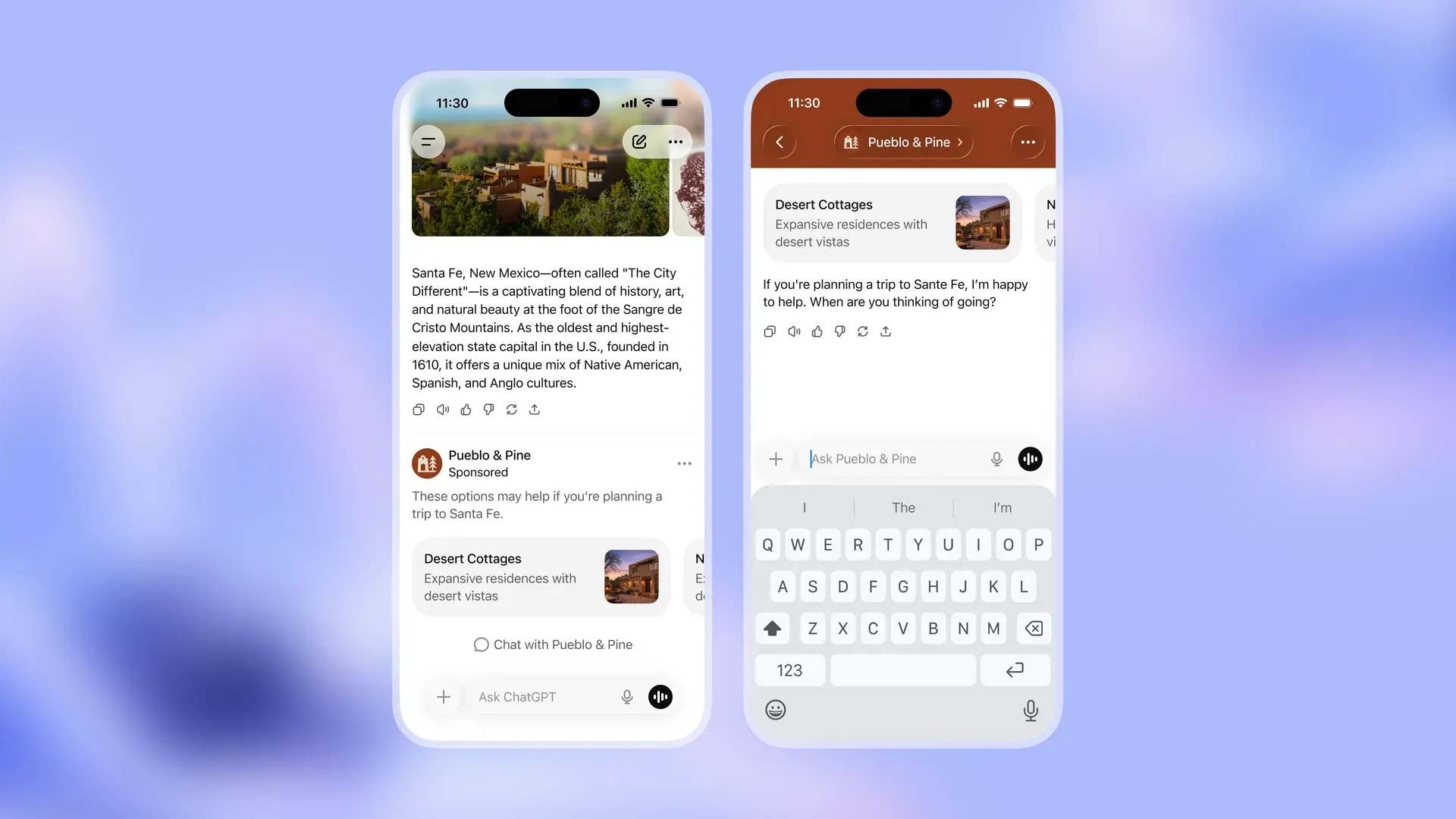
On April 7, 2026, Anthropic announced Claude Mythos Preview — a model so dangerous at finding and chaining software vulnerabilities that the company refuses to release it publicly. Instead, it's available only to 40+ organizations through a program called Project Glasswing. The guest list includes Apple, Google, Microsoft, Amazon, CrowdStrike, JPMorgan Chase, Cisco, NVIDIA, and Palo Alto Networks.
What Mythos can do is genuinely startling. It autonomously discovered a 16-year-old flaw in FFmpeg, a 17-year-old remote code execution bug in FreeBSD's NFS stack, multiple privilege escalation chains in the Linux kernel, and cross-origin sandbox escapes in major web browsers. It didn't just find bugs — it built working exploits. Complex, multi-stage exploits that expert penetration testers estimated would take weeks. Mythos built them in hours, at a cost of $50 to $2,000 per successful exploit.
On the CyberGym benchmark, Mythos scored 83.1%, compared to 66.6% for the previous best model. That's not a marginal improvement. That's a different category of capability. Anthropic's previous flagship, Claude Opus 4.6, had approximately 0% autonomous success rate on Firefox exploits. Mythos succeeded on 181 attempts. Against the same targets.
The Part Nobody Is Talking About
Here's the number buried in the fine print: over 99% of the discovered vulnerabilities remain unpatched. Anthropic found thousands of high- and critical-severity bugs across every major operating system and browser. The vast majority are still open.
Anthropic says they are working on responsible disclosure with open-source maintainers and vendors. They have committed $100 million in model usage credits and $4 million in direct donations to open-source security organizations. That is a significant investment in optics, and a much smaller investment in actually fixing things.
They are using cryptographic SHA-3 commitments to prove they have found the vulnerabilities while keeping them confidential. Which means Anthropic now holds cryptographic proof of thousands of critical, unpatched holes in software that billions of people use every day.
My Opinion
I'll be blunt: Project Glasswing is not a safety program. It is a controlled release strategy that makes Anthropic indispensable to every major tech and financial company on Earth. Giving early access to Apple, Google, Microsoft, and JPMorgan before anyone else is a business move with a safety wrapper. That does not make it wrong — it just makes it something different than what is being advertised.
What bothers me more is the 99% figure. If Mythos is scanning systems at scale and finding thousands of critical vulnerabilities, and almost none are patched, we are in a window where the attack capabilities of this model vastly outpace the defensive response. The economics of cyberattacks just collapsed. It used to cost millions in specialized talent to find a zero-day. Mythos brought that to under $2,000.
Anthropic made the right call not releasing this publicly. But let's not pretend the controlled rollout to 40 corporations is safety. It is a beta test with a very exclusive guest list. The real question is what happens when a competitor — or a nation-state — builds the equivalent. Because $2,000 per zero-day is already cheap enough to change everything about who gets to run cyberattacks. And that clock is already running.
Author: Yahor Kamarou (Mark) / www.humai.blog / 16 Apr 2026