Anthropic's Claude Mythos Preview has found thousands of previously unknown vulnerabilities in every major operating system and every major web browser. Some of those bugs are decades old, engineers at partner organizations are working to patch them, and less than 1% have been fixed so far.
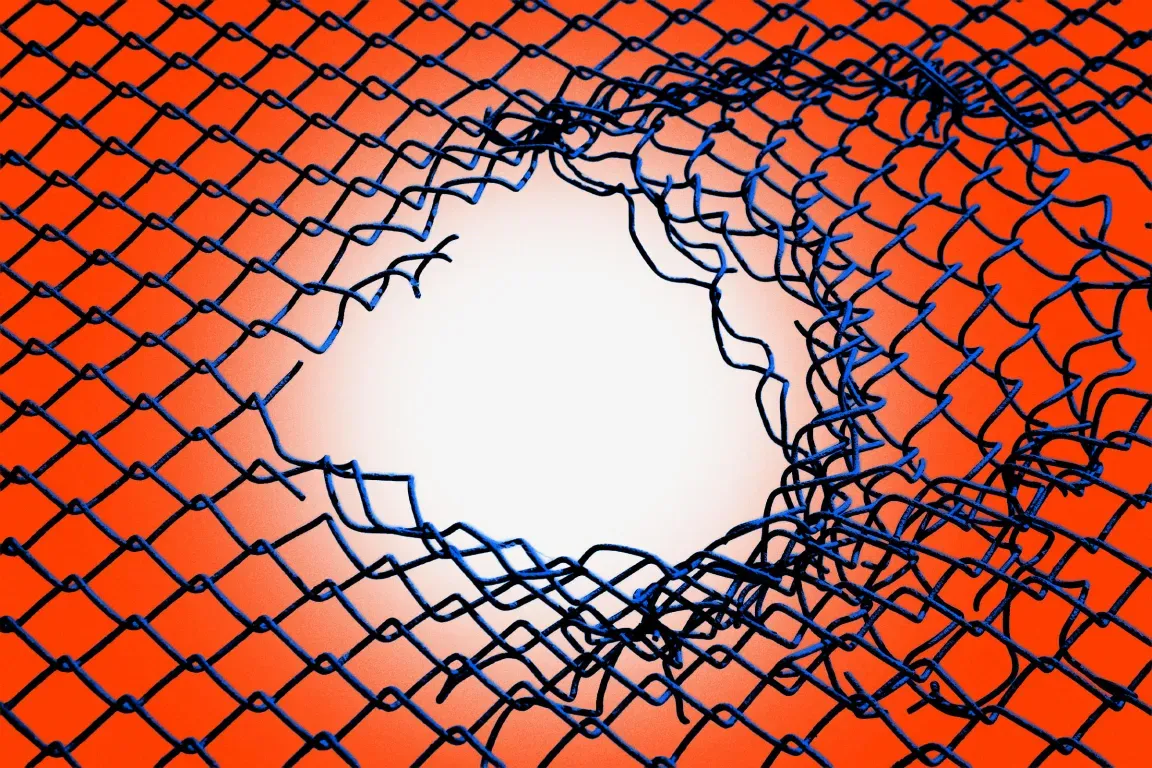
That figure, disclosed in Anthropic's technical documentation for Project Glasswing, defines the challenge at the center of the initiative. The model's discovery rate has outpaced the patch rate by several orders of magnitude, and the window between discovery and potential exploitation by others narrows every month as AI capabilities spread beyond the organizations committed to using them responsibly.
Project Glasswing is Anthropic's response: a coordinated, $100 million defensive cybersecurity program that gives twelve of the world's most important technology companies exclusive access to Mythos Preview, with a single mandate to find and fix critical vulnerabilities before adversaries develop comparable capabilities.
What the Model Found
Claude Mythos Preview was pointed at production codebases over a period of roughly four weeks before the April 7, 2026 announcement. The methodology is deliberately straightforward: launch an isolated container running a target codebase, invoke the model with a prompt to find a security vulnerability, and let it work without further human guidance. The model reads code, forms hypotheses about what might be broken, runs the software to test those hypotheses, uses debuggers as needed, and produces a bug report with a working proof-of-concept exploit.
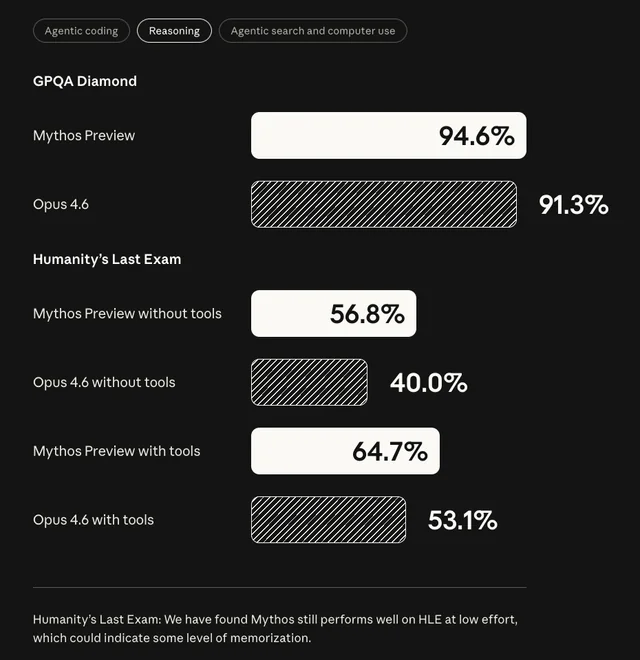
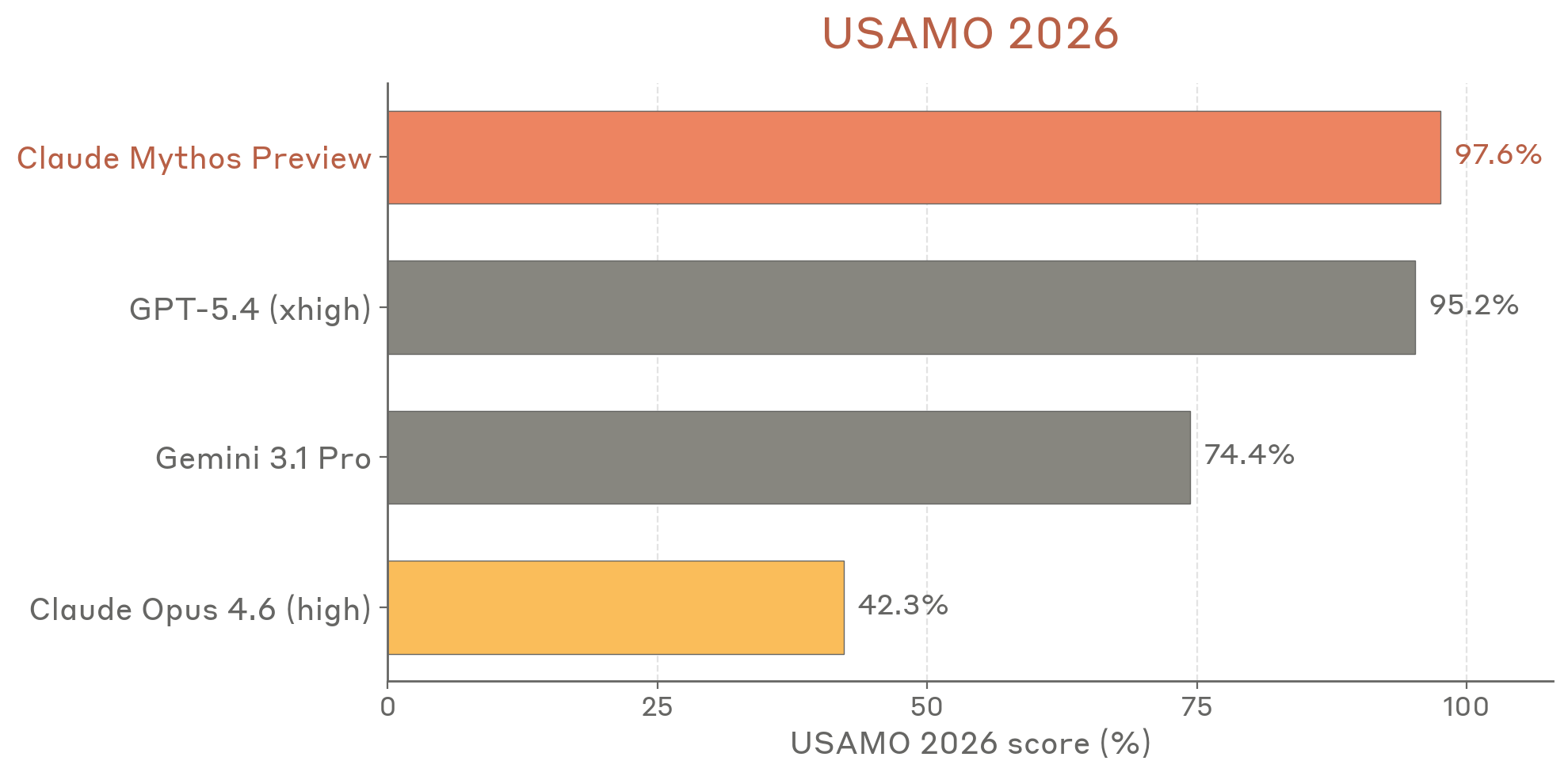
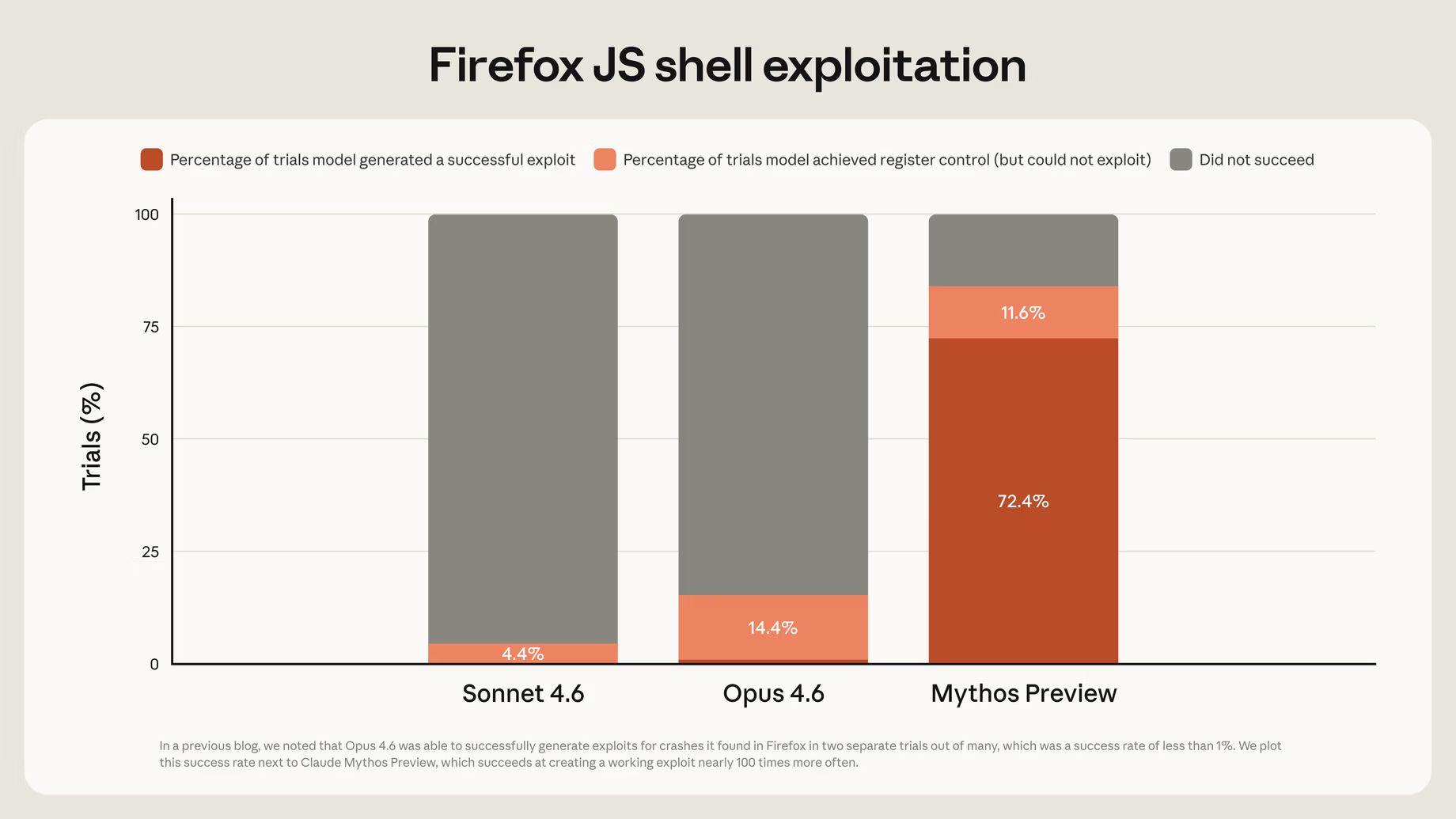
The results, described in Anthropic's red team blog, represent the most extensive autonomous vulnerability discovery effort ever published by an AI lab.
Anthropic notes that fewer than 1% of discovered vulnerabilities have been publicly disclosed, because doing so before patches are available would be irresponsible. Of the subset that have been patched and can be described, three cases illustrate the model's capabilities:
The 99% Problem
The disclosed cases are the easy part: bugs that have been patched and can be discussed openly. The vast majority of what Mythos found cannot be disclosed yet, because the patches do not exist.
Anthropic has committed to publishing a public report within 90 days of the April 7 launch, landing in early July 2026, summarizing what Glasswing has fixed and what the industry has learned. That timeline reflects the coordinated disclosure framework Glasswing operates under: bugs are reported to the affected organization, a remediation window is provided, and the vulnerability details are released only after a patch ships.
The problem is one of arithmetic: thousands of vulnerabilities, a handful of major partners, and patching processes that operate at human speed. Picus Security's CTO Volkan Erturk put it directly at the 2026 FS-ISAC Americas Spring Summit: defenders must work at calendar speed while attacks happen at machine speed.
Anthropic's own red team blog acknowledges the mismatch: "Over 99% of the vulnerabilities we've found have not yet been patched, so it would be irresponsible for us to disclose details about them. Yet even the 1% of bugs we are able to discuss give a clear picture of a substantial leap in what we believe to be the next generation of models' cybersecurity capabilities."
How Project Glasswing Works
Project Glasswing launched April 7, 2026, with twelve named partners and access extended to more than 40 additional organizations that build or maintain critical software infrastructure.
The Named Partners
The twelve launch partners are Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, NVIDIA, Palo Alto Networks, and Anthropic itself. Four additional partners have not been publicly named, though reporting indicates they include organizations responsible for critical open-source infrastructure.

These are not pilot customers experimenting with AI but the organizations that build the operating systems, browsers, cloud platforms, and security tools that the rest of the software industry runs on. When Microsoft's team finds and patches a vulnerability in Windows, that fix ships to every Windows user in the world.
The Rules
The governance structure is specific and non-negotiable. Partners may use Mythos Preview exclusively for finding and fixing vulnerabilities in software they own or maintain. All discoveries go through Anthropic's 90+45 day coordinated disclosure process. Anthropic retains operational oversight and can revoke access for any violation. The model runs in sandboxed environments with restricted network access and detailed logging.
Partners are not permitted to use Mythos offensively, to share findings beyond their own remediation teams, or to use access for any purpose outside the defined defensive scope.
The Funding
Anthropic has committed $100 million in Mythos Preview usage credits to the initiative, so partners do not pay API fees for their security work. An additional $4 million in direct donations goes to open-source security organizations: $2.5 million to Alpha-Omega and OpenSSF through the Linux Foundation, and $1.5 million to the Apache Software Foundation.
After the research preview concludes, Mythos Preview will be available to partners through the Claude API, Amazon Bedrock, Google Cloud Vertex AI, and Microsoft Foundry at $25 per million input tokens and $125 per million output tokens.
Why the Partners Are Treating This as Urgent
The statements from Glasswing's launch partners are notable for their directness. These are companies with large legal and communications teams that typically produce careful, hedged public statements. The language here is different.
Cisco's statement: "AI capabilities have crossed a threshold that fundamentally changes the urgency required to protect critical infrastructure from cyber threats, and there is no going back. The old ways of hardening systems are no longer sufficient. Providers of technology must aggressively adopt new approaches now."
Microsoft's statement, from EVP of Cybersecurity and Microsoft Research Igor Tsyganskiy: "The window between a vulnerability being discovered and being exploited by an adversary has collapsed. What once took months now happens in minutes with AI. Claude Mythos Preview demonstrates what is now possible for defenders at scale, and adversaries will inevitably look to exploit the same capabilities."
AWS CISO Amy Herzog: "AI capabilities have crossed a threshold that fundamentally changes the urgency required to protect critical infrastructure from cyber threats. Our foundational work with these models has shown we can identify and fix security vulnerabilities across hardware and software at a pace and scale previously impossible."
The consistency of tone across organizations that rarely speak with this kind of urgency suggests the findings from Mythos Preview have produced genuine alarm inside the world's largest software companies, not just useful marketing material for a security initiative.
Why Mythos Finds What Decades of Review Missed
Understanding why AI finds bugs that 27 years of expert human review missed requires understanding what the old approach was missing.
Traditional automated security tools, primarily fuzzers, work by generating massive volumes of random inputs and observing what causes the software to crash. Fuzzing is effective at finding bugs caused by unexpected inputs in code that processes external data, but it does not read code and cannot reason about what the developer intended, what assumption was made in 2003 that is no longer valid, or how a subtle type error introduced in one commit might interact with a refactoring three years later.
Mythos reads and reasons about code. Anthropic's red team describes the standard workflow: the model scans the codebase, examines previous patch commits to look for related unaddressed issues, identifies patterns associated with known vulnerability classes, and constructs the specific input that would trigger the bug. It then runs the software to validate the hypothesis and produces a working proof-of-concept.
This is how a skilled human security researcher approaches a codebase, applied at machine speed and without fatigue. The FFmpeg bug that automated tools hit five million times without noticing required understanding the relationship between a 2003 design decision and a 2010 code change, which is a reasoning task rather than a pattern-matching task and precisely the category of work that current AI models can perform.
Anthropic's assessment of how this capability emerged is significant: "We did not explicitly train Mythos Preview to have these capabilities. Rather, they emerged as a downstream consequence of general improvements in code, reasoning, and autonomy." The cybersecurity capability is not a feature that was engineered but a consequence of the model becoming generally better at understanding code, meaning every improvement in general capability also improves the model's ability to find and exploit security flaws.
What This Means for Software That Is Not Inside Glasswing
Project Glasswing covers twelve major partners and roughly 40 additional organizations, which is a large coalition but still a small slice of the world's software ecosystem.
Anthropic has explicitly addressed the gap. Every vulnerability Mythos finds in Linux, Firefox, Windows, or macOS, and then gets patched by a Glasswing partner, produces a fix that ships downstream to every developer and every user who depends on that software. The FreeBSD patch benefits every FreeBSD deployment in the world. The OpenBSD fix ships to every firewall and critical infrastructure component running that OS.
For developers and organizations outside the partner network, three practical implications follow directly from Glasswing's timeline and scope.
Patch cycles matter more now than they ever have. The 90-day disclosure window Glasswing operates under means a wave of security patches will begin shipping in earnest around July 2026. Organizations with slow or informal patching processes should treat that timeline as a planning horizon.
Dependency security is not a theoretical concern. The codebases Mythos is scanning include the operating systems, browsers, media codecs, network stacks, and cryptographic libraries that form the dependency trees of most production software. Vulnerabilities found and patched in those libraries will flow as updates. Organizations that auto-update dependencies will receive those protections automatically. Organizations that manually manage dependencies or run pinned versions should plan for a significant round of security updates.
Open-source maintainers who are not inside the partner network can apply for access through Anthropic's Claude for Open Source program, which extends Mythos access to maintainers of qualifying critical open-source projects.
The Broader Question Glasswing Raises
Project Glasswing is explicitly framed as a transitional measure. Anthropic's stated goal is not to keep Mythos restricted permanently but to give defenders enough time to patch the most critical vulnerabilities before similar capabilities become widely available to actors who will not operate under the same constraints.
Logan Graham, who leads offensive cyber research at Anthropic, estimates six to eighteen months before comparable capabilities proliferate beyond organizations committed to responsible deployment, a narrow and uncertain window given that the same tools Mythos uses for defensive scanning are tools that a motivated state actor or organized criminal group would use for offensive exploitation.
Cisco's framing captures the structural reality: "There is no going back." AI has changed the floor of what is possible in vulnerability research, not just the ceiling. The security industry's prior posture, relying on manual review and fuzzing while treating the difficulty of human-speed research as a partial defense, describes an era that is ending.
Project Glasswing is the opening move of a different era, and whether the patching pace can keep up with the discovery pace, whether the 90-day disclosure timeline holds against the volume of findings, and whether the defensive window Anthropic describes is real and long enough to matter are questions the July 2026 report will begin to answer.
Conclusion
The number that defines Project Glasswing is not the $100 million in usage credits, not the twelve named partners, and not the forty additional organizations. It is the less-than-1% patch rate.
Claude Mythos Preview found thousands of critical vulnerabilities in the software that the world's infrastructure runs on, including bugs that survived 27 years of expert review and five million automated test runs, and produced working exploits in hours.
The vast majority of what it found is still unpatched, sitting in codebases that millions of people depend on, waiting for the patching process to catch up. The urgency behind every partner statement, every carefully governed access restriction, and every dollar of usage credits comes from one operational reality: there is a finite window between when Mythos found these vulnerabilities and when something else will find them too.
Frequently Asked Questions
What is Project Glasswing?
Project Glasswing is a defensive cybersecurity initiative launched by Anthropic on April 7, 2026. It provides Claude Mythos Preview, an unreleased frontier AI model, to twelve major technology and security organizations, including Amazon, Apple, Google, Microsoft, and the Linux Foundation, plus more than 40 additional critical-software maintainers. Partners use the model exclusively to find and fix vulnerabilities in software they own or maintain. Anthropic has committed $100 million in usage credits and $4 million in donations to open-source security organizations.
Why are less than 1% of the discovered vulnerabilities patched?
Mythos Preview has found thousands of zero-day vulnerabilities across every major operating system and browser over roughly four weeks of testing. Patching at that scale requires coordinated disclosure with affected vendors, engineering time to develop and test fixes, and release processes that take weeks to months per patch. The discovery rate has outpaced the patching rate significantly. Anthropic operates a 90+45 day disclosure timeline, and a public report summarizing what Glasswing has fixed is expected in early July 2026.
Which specific vulnerabilities has Project Glasswing found?
Anthropic has disclosed only the small fraction of findings that have already been patched. These include a 27-year-old denial-of-service vulnerability in OpenBSD, a 17-year-old remote code execution vulnerability in FreeBSD's NFS server (CVE-2026-4747) that allows unauthenticated root access, and a 16-year-old vulnerability in the FFmpeg video codec. Browser exploit chains chaining four or more vulnerabilities have also been documented. Over 99% of findings remain undisclosed pending patches.
Who are the Project Glasswing partners?
The twelve named launch partners are Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, NVIDIA, Palo Alto Networks, and Anthropic. More than 40 additional organizations that build or maintain critical software infrastructure have also been granted access. Four partners have not been publicly named.
Can organizations outside the partner network benefit from Project Glasswing?
Yes, indirectly. Every vulnerability patched by a Glasswing partner ships as an update available to all users of that software. The OpenBSD, FreeBSD, and FFmpeg patches benefit every deployment of those systems globally. Open-source maintainers of qualifying critical projects can also apply for access through Anthropic's Claude for Open Source program.
When will the full results of Project Glasswing be publicly available?
Anthropic has committed to publishing a public report within 90 days of the April 7, 2026 launch, expected in early July 2026. The report will cover what has been fixed, what the participants have learned, and which vulnerabilities can be disclosed. Anthropic has also committed to producing practical recommendations for how security practices should evolve in the AI era, developed in collaboration with leading security organizations.
Related Articles